
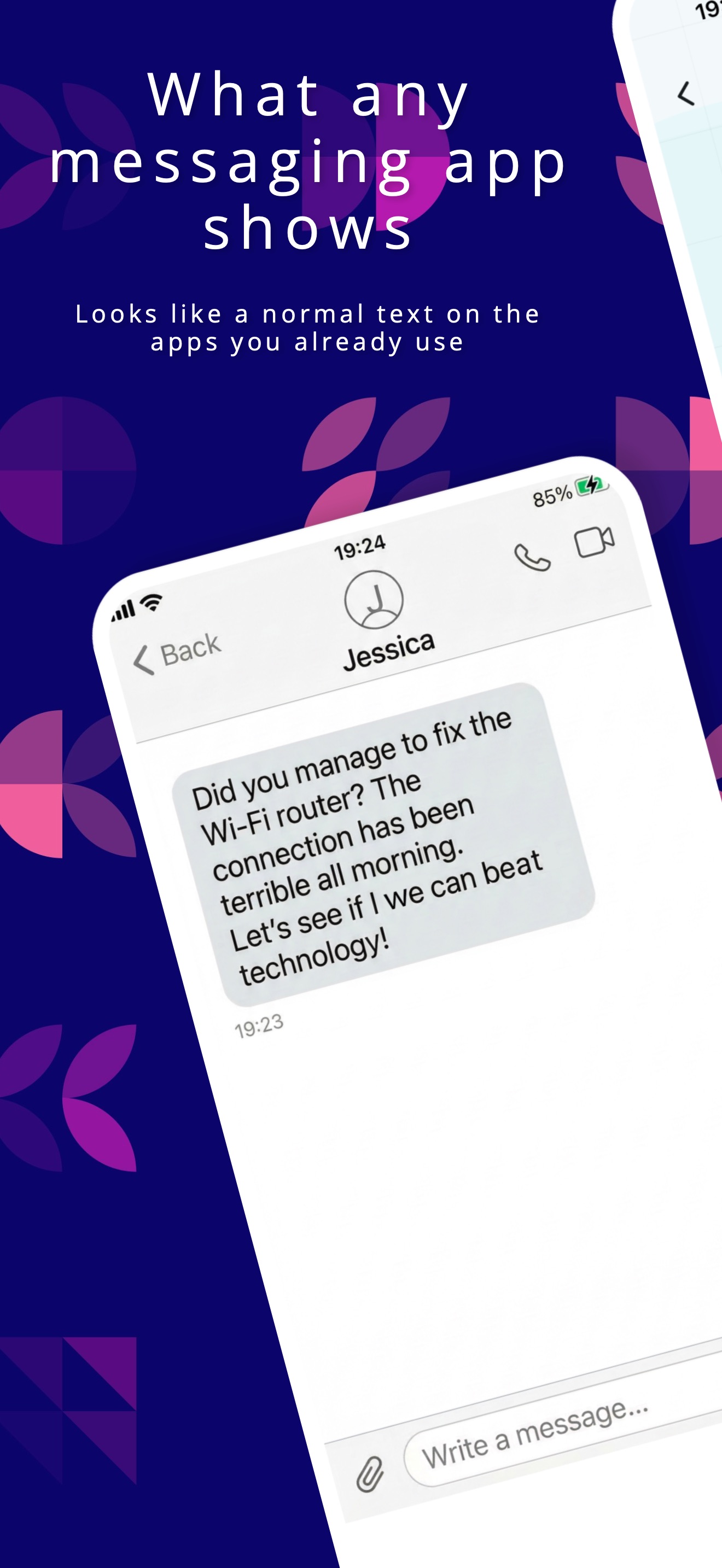
Layergram lets you send end‑to‑end encrypted messages over WhatsApp, Telegram, Signal, SMS, email, or any text‑based app – using invisible Unicode characters.

Layergram encrypts your message end‑to‑end using modern cryptography (X25519 + AES‑GCM).
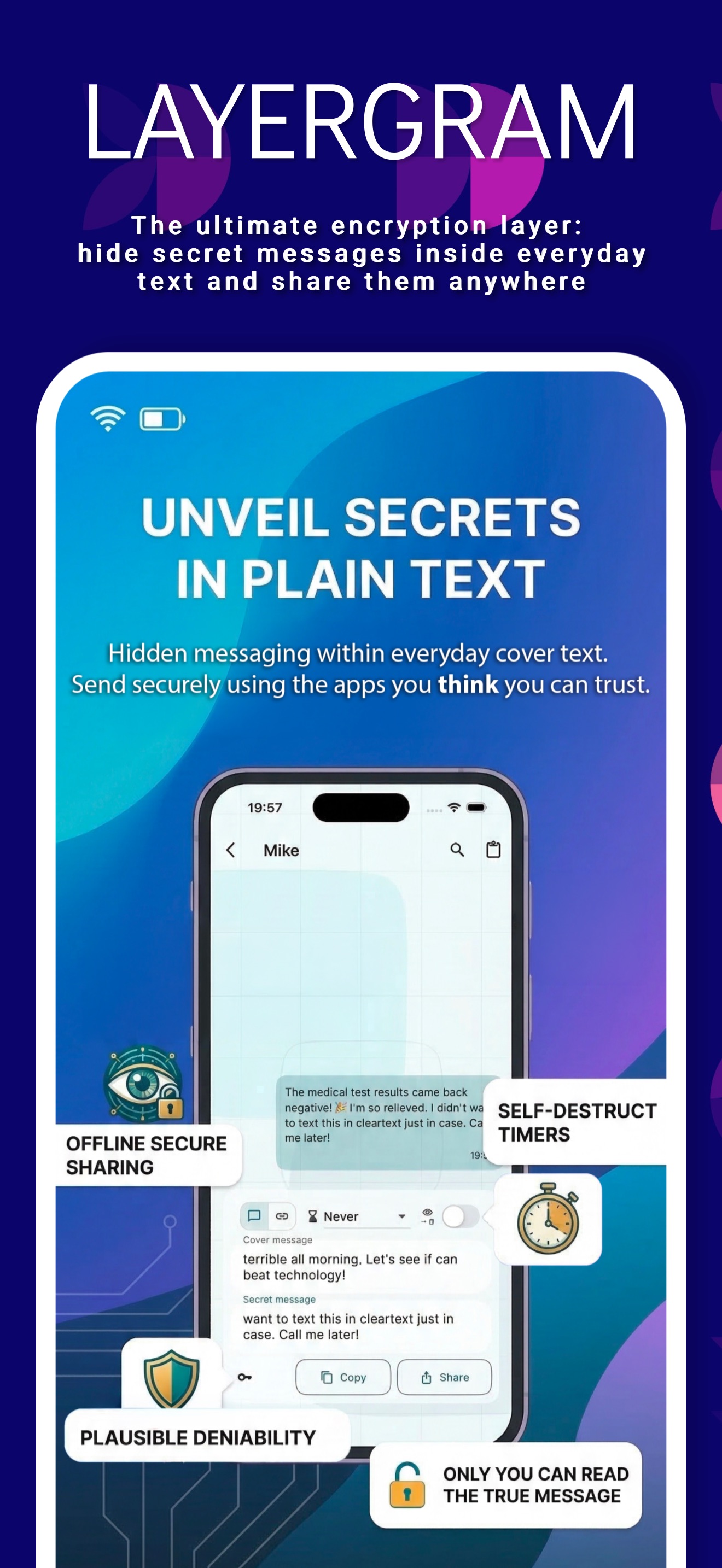
The raw encrypted bytes are mixed with random noise and encoded into zero‑width Unicode characters, then interleaved into a normal cover message.
You paste and send that text via any messaging app. Only Layergram clients with the right keys can trial-decrypt and reveal the hidden message.
Transport-agnostic by design. Works over: WhatsApp, Telegram, Signal, iMessage, SMS, Email, Forums, and more.

3 taps to share an encrypted message from Layergram directly to a contact in your favorite chat app. 2 taps to share a received message back to Layergram and reveal the hidden payload. No manual copy-pasting of ciphertexts required.
Official Layergram releases are available on mobile and desktop. Linux remains source-build friendly, and web is intentionally not distributed in this release.
Official release
Official release
Official release
Official release
Compilable from source
Not distributed in this release
Your privacy shouldn't depend on the transport layer's promises. Keys never leave your device.
To the human eye, your communication looks like standard text. While automated analysis can detect zero-width characters, casual observers only see an innocent conversation.
Use the same encryption standard whether you are sending an SMS or posting on a public forum.
We don't operate servers to route your messages. You leverage the platforms you already use, eliminating a single point of failure.
Layergram does not require a phone number or email address. Your identity is simply a locally generated cryptographic key.
Auditable security. The cryptography and message format are completely open for review.
Layergram is built to protect your most sensitive daily communications. With built-in anti-screenshot protection and biometric/PIN locks, your secrets stay safe. Furthermore, thanks to steganography, underlying transport apps cannot read your hidden payload. Layergram's signature-less encoding ensures the data remains mathematically indistinguishable from random noise.
Note: Your private keys never leave your device. There is no central Layergram server that can read, route, or intercept your messages.
Read the Layergram Message Format (LMF) spec →An optional feature for extreme privacy. Set an expellable passphrase to unlock completely hidden identities. If forced to hand over your device, hidden messages remain mathematically indistinguishable from abandoned data.
Learn how Plausible Deniability works
Your private keys are yours alone. Back them up securely using a standard sequence of words (BIP39).
This public repository contains the official Layergram Flutter app, the Layergram Message Format specification, and the local encryption, identity, steganography, and storage logic.
Is Layergram a new messenger?
No. It is an encryption layer that uses your existing messengers as the transport medium.
Can platforms detect my hidden messages?
Automated filters can detect invisible characters. However, Layergram uses signature-less binary payloads combined with random noise injection. The hidden data is mathematically indistinguishable from random noise.
Does Layergram run a central server?
No. Keys remain entirely local on your device. You use existing networks to send messages and they cannot access your keys.
Can you recover my 24-word recovery key if I lose it?
No. Your 24-word recovery key is private, secret, and never leaves your control. We do not store it, we cannot recover it, and you should never share it with anyone. Layergram will never ask you to send it.
Why can't I find the "Share" button on Android?
Because of Android platform limitations, Layergram cannot reliably pass the complete message package (cover text plus hidden secret) directly to another app. You can still use Copy and paste it into the destination app. We are evaluating better options for future releases.
Can I use the same identity on multiple devices?
Yes. Import the same recovery key on each device to use the same identity for sending and receiving messages. Messages themselves are not synced between devices, so each device keeps its own local history.